When a security event is detected in remote video monitoring, a precise sequence unfolds: AI flags the activity, a live operator reviews and assesses it within seconds, a verbal warning is issued if the situation warrants, and law enforcement is contacted with verified footage if the individual does not comply. This process, from detection to response, typically takes less than 60 seconds.
Inside the Response: What Happens When Remote Monitoring Detects a Threat
Many businesses understand that remote video monitoring helps prevent crime, but fewer know what actually happens behind the scenes when suspicious activity occurs.
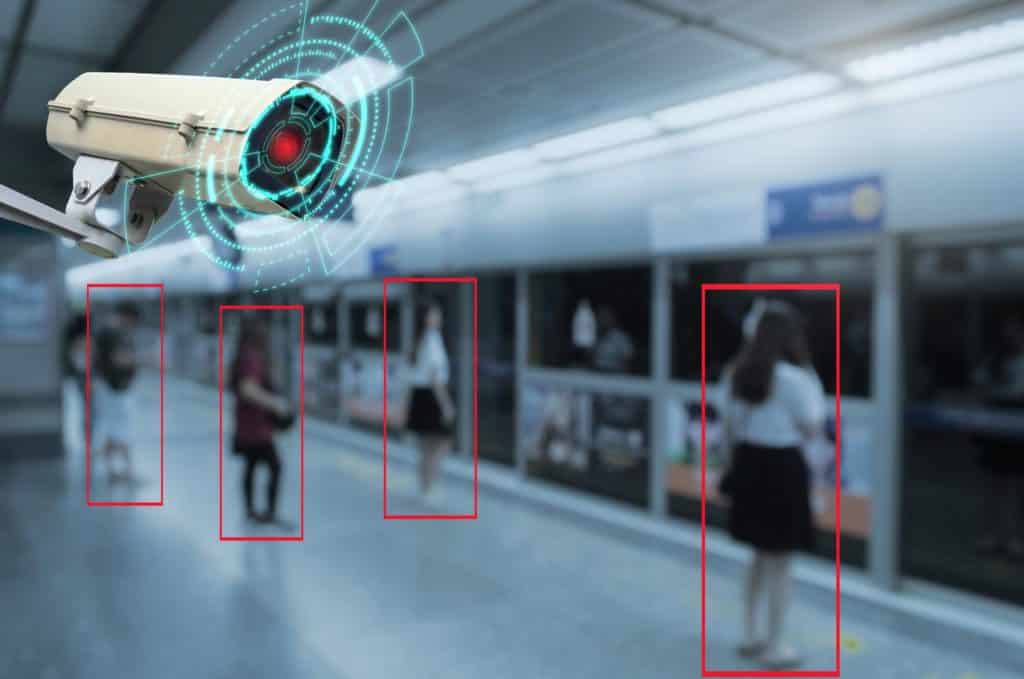
Remote video monitoring is not just cameras recording video. It is a coordinated process where technology detects activity and trained professionals respond in real time.
Understanding this step-by-step process helps explain why remote video monitoring is effective at stopping incidents before they escalate.
Step 1: AI Detects Suspicious Activity
The process begins with AI-enabled cameras positioned across a property. These cameras continuously evaluate activity and are configured to focus on specific areas such as:
- Entrances and exits
- Perimeter fencing
- Equipment or material storage areas
- Parking lots or vehicle rows
When movement occurs in restricted areas or at unusual times, the system flags the activity as a potential security event. This helps reduce false alarms by focusing only on activity that may require attention.
Step 2: A Monitoring Agent Reviews the Event
Once activity is flagged, the event is immediately sent to a security operations center where a trained monitoring agent reviews the footage.
At this stage, the agent determines:
- What is happening on the property
- Whether the activity is authorized or suspicious
- Whether intervention is needed
This human verification step is critical because it ensures that responses are based on real situations, not just motion detection. But not all security operations centers are equal: when evaluating a remote video monitoring partner, look for the center to be both UL-Certified and having the Five Diamonds designation from The Monitoring Association. Companies, such as Pro-Vigil, have these certifications that provide assurance that their monitoring staff is trained and using the best practices.
Step 3: Real-Time Deterrence Is Deployed
If the activity appears suspicious, the monitoring agent can respond immediately. Common deterrents include:
- Loud sirens or audio deterrents
- Flashing lights or security alarms
These responses are designed to make it clear that the property is actively monitored. In many cases, this is enough to stop the activity. When individuals realize someone is watching and responding, they often leave before any damage or theft occurs.
Step 4: Escalation to Authorities if Needed
If the individual does not leave the property or the situation escalates, the monitoring agent can contact local law enforcement.
Because the event has already been reviewed and verified, a major benefit of remote video monitoring compared to typical alarm systems, the information provided to authorities is more accurate than a typical unverified alarm. This can include:
- A description of the individual or vehicle
- Real-time updates on the situation
- Confirmation that the activity is unauthorized
This verified response helps improve the effectiveness of police dispatch.
Step 5: Video Is Stored for Investigations
Throughout the entire process, the system records and stores high-definition footage of the event. This recorded video can be used to:
- Review what happened on the property
- Provide evidence to law enforcement
- Support insurance claims or internal investigations
This ensures that even if an incident occurs, businesses have access to clear documentation. Furthermore, if the business has license plate recognition cameras in tandem with their remote video monitoring system, they will be able to gain insights into the times and license plates of the vehicles that accessed their site.
Why This Process Matters
The strength of remote video monitoring comes from how these steps work together. Instead of relying on a single trigger or delayed response, the system:
- Detects activity using AI
- Verifies the situation with a monitoring agent
- Responds in real time with deterrents
- Escalates when necessary
- Records everything for later review
This coordinated approach allows businesses to move from reacting to incidents to preventing them altogether.
A Smarter Way to Protect Your Property
Security events can unfold quickly, especially after hours when properties are unattended.
Remote video monitoring provides a structured, real-time response process that helps stop incidents before they cause damage while still capturing the footage needed for investigations.
Companies such as Pro-Vigil use this approach to protect construction sites, dealerships, commercial properties, and other high-risk environments, helping businesses detect suspicious activity, respond immediately, and maintain visibility into what is happening on their property.
Frequently Asked Questions
Live monitoring operators typically assess and respond to AI-flagged alerts within 30 to 60 seconds of detection. This response time is far faster than waiting for a motion alert to reach a property owner’s phone, faster than a guard reaching an incident location, and faster than the typical law enforcement response to an unverified alarm call.
The operator first reviews the footage to determine whether the activity is a genuine security concern. If it is, they issue a verbal warning through on-site speakers, identifying that the property is monitored and that the individual should leave immediately. If the person does not comply, the operator escalates to law enforcement, providing a real-time description and verified video to support a credible response.
Yes. Professional remote monitoring providers maintain protocols for law enforcement notification and operators can contact police directly when a situation warrants escalation. Because the operator can confirm that an incident is actively occurring and provide a real-time description of the individuals involved, verified monitoring calls receive priority over standard unverified alarm calls in most jurisdictions.
A two-way audio warning is when a monitoring operator speaks directly to an individual on the monitored property through speakers mounted on or near the camera unit. The message typically identifies that the property is monitored, that the operator can see the individual, and that they should leave immediately. This direct communication is one of the most effective deterrents available in remote monitoring, most people leave immediately when addressed this way.
Footage is typically stored on secure cloud servers or on-device storage and retained for a defined period, commonly 30 to 90 days, depending on the provider and service level. Incident footage is flagged and can be retrieved by the property owner, management team, or law enforcement through a secure client portal. This documentation supports investigations, insurance claims, and legal proceedings.